BREAKINGBy Xavier Rivera· ·1 min read
Storm-1175 Blitzes Web Vulns with Medusa Ransomware
Microsoft reveals Storm-1175 ransomware group rapidly exploits new web-facing vulnerabilities for Medusa deployments and data exfil. The high-velocity tactics shrink patching windows to days, forcing orgs to prioritize internet-exposed assets amid surging ransomware threats.
Source:Microsoft Security Blog
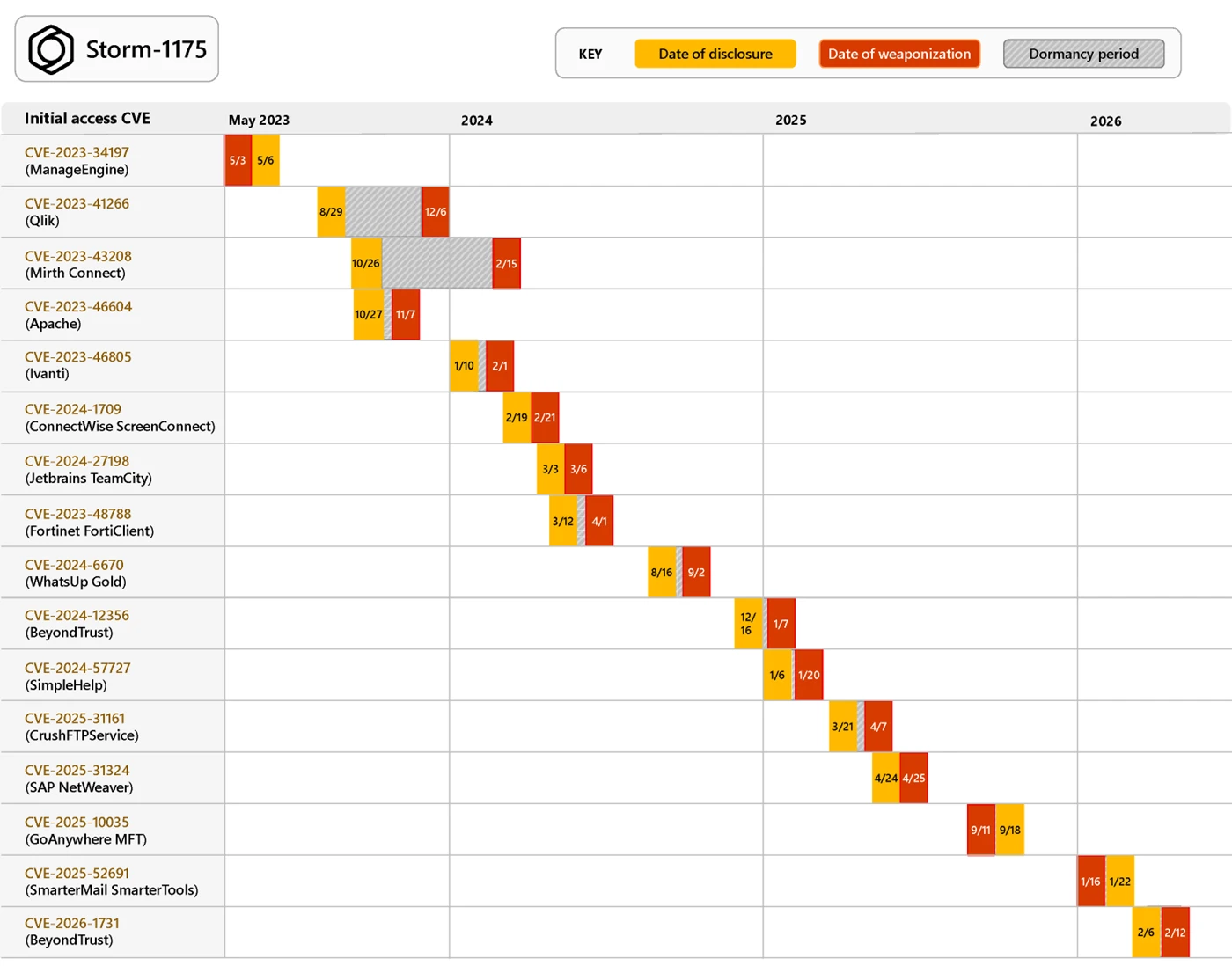
Storm-1175, a ruthless ransomware crew, pounces on freshly disclosed vulnerabilities in web-facing assets, turning days-old flaws into footholds for data theft and Medusa deployment. Microsoft tracks the group's high-tempo ops, where initial access leads straight to exfiltration and ransomware drops like Gaze.exe—all in a blistering pace that leaves defenders scrambling.
These attacks zero in on internet-exposed servers, exploiting bugs in software like unpatched web apps or misconfigured portals. Storm-1175's playbook skips slow reconnaissance; they scan broadly, weaponize vulns within 48 hours of disclosure, and hit victims across sectors. Medusa, their ransomware of choice, encrypts files while threatening leaks, amplifying pressure on payments.
The velocity sets Storm-1175 apart from lumbering state actors. Where others probe for months, this financially driven group iterates daily, adapting to patches and countermeasures. Microsoft notes their use of legitimate tools for evasion, blending into noisy enterprise environments.
Organizations face a shrinking defense window. Web-facing assets—think IIS servers, APIs, or remote management interfaces—represent low-hanging fruit amid rising ransomware claims, which topped $1B in 2023 per Chainalysis. Competitors like LockBit evolve similarly, but Storm-1175's speed signals a new norm in commodity cybercrime.
Expect escalation as vuln disclosures surge; CISA logged 1,200+ CVEs last quarter alone. Enterprises must shift from reactive patching to zero-trust segmentation and continuous vulnerability scanning. Storm-1175 proves fast exploitation now trumps sophistication—prompting a reevaluation of external attack surfaces everywhere.
These attacks zero in on internet-exposed servers, exploiting bugs in software like unpatched web apps or misconfigured portals. Storm-1175's playbook skips slow reconnaissance; they scan broadly, weaponize vulns within 48 hours of disclosure, and hit victims across sectors. Medusa, their ransomware of choice, encrypts files while threatening leaks, amplifying pressure on payments.
The velocity sets Storm-1175 apart from lumbering state actors. Where others probe for months, this financially driven group iterates daily, adapting to patches and countermeasures. Microsoft notes their use of legitimate tools for evasion, blending into noisy enterprise environments.
Organizations face a shrinking defense window. Web-facing assets—think IIS servers, APIs, or remote management interfaces—represent low-hanging fruit amid rising ransomware claims, which topped $1B in 2023 per Chainalysis. Competitors like LockBit evolve similarly, but Storm-1175's speed signals a new norm in commodity cybercrime.
Expect escalation as vuln disclosures surge; CISA logged 1,200+ CVEs last quarter alone. Enterprises must shift from reactive patching to zero-trust segmentation and continuous vulnerability scanning. Storm-1175 proves fast exploitation now trumps sophistication—prompting a reevaluation of external attack surfaces everywhere.
EXPERT TAKE
Expert Take: Azure admins, deploy Microsoft Defender for Cloud's auto-remediation for web apps and enable just-in-time access on VMs to block Storm-1175-style rapid exploits.
cybersecurityransomwareMicrosoftMedusa